Repressive governments buy cheap spyware to keep tabs on critics
Spyware is now a growing business giving less technically advanced nations a surveillance edge
Ethiopian journalist Mesay Mekonnen was at his desk at a news service based in the US when gibberish skittered across his computer screen in December. A sophisticated cyberattack was under way.

The likely culprits were government hackers from a much less technically advanced nation, Ethiopia, where the perpetrators apparently bought commercial spyware off the shelf, a non-profit research lab says.
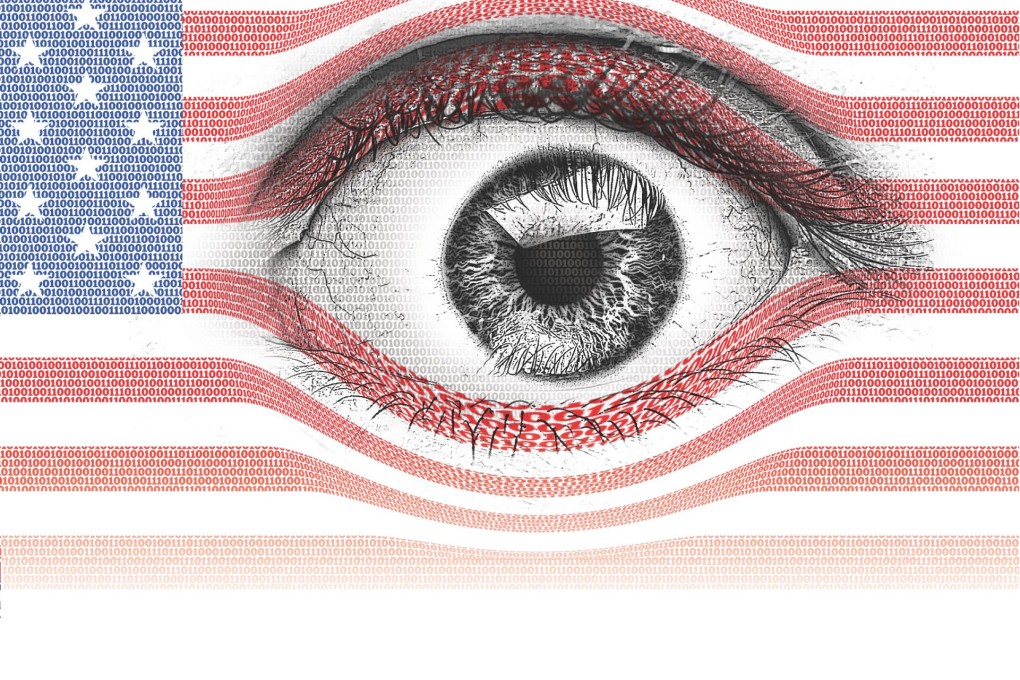
Once the exclusive province of the most elite spy agencies like the National Security Agency, spyware is now a growing commercial industry, making surveillance capabilities widely available to governments worldwide.
The targets often are political activists, human rights workers and journalists who have learned that the internet allows authoritarian governments to watch and intimidate them, even after they have fled to supposedly safe havens.
That includes the United States, where laws prohibit unauthorised hacking but rarely stop intrusions. The trade in spyware itself is almost entirely unregulated, to the critics' frustration.