Singapore was the top cyber attack target during Trump-Kim talks, says report
Eighty-eight per cent of the 40,000 attacks were launched from Russia

By Cynthia Choo
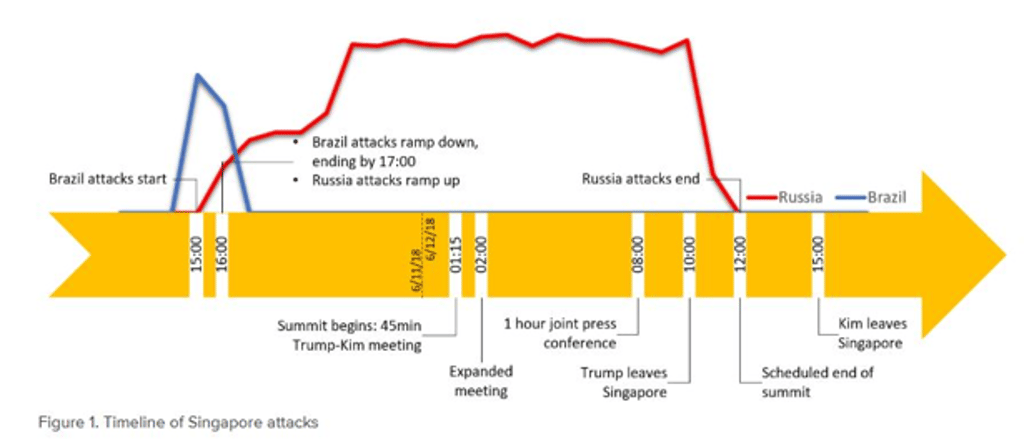
Singapore was the top cyber attack target around the world during the Trump-Kim summit, with the country experiencing close to 40,000 attacks during the June 12 meeting, according to data collected by American technology company F5 Networks and its data partner Loryka.
Data analysis by F5 Networks’ Threat Research Intelligence team, which monitors global attacks, found that cyber attacks “skyrocketed” from June 11 and 12.Eighty-eight per cent of the 40,000 attacks were launched from Russia, followed by eight per cent from Brazil, and two per cent from Germany.
In addition, 97 per cent of all attacks from Russia during the two-day period were targeted at Singapore, said F5 Network’s report which was published on June 14. The company could not verify if the attacks were state sponsored.
Singapore also received up to 4.5 times more attacks than the United States or Canada on both days.