Super Micro tells US lawmakers it found no Chinese spy chips, denying Bloomberg report
- Server maker says ‘recent Bloomberg Businessweek stories are wrong’ in letter to US senators
- ‘It is impossible as a practical matter to insert unauthorised malicious chips onto our boards during manufacturing,’ senior exec writes
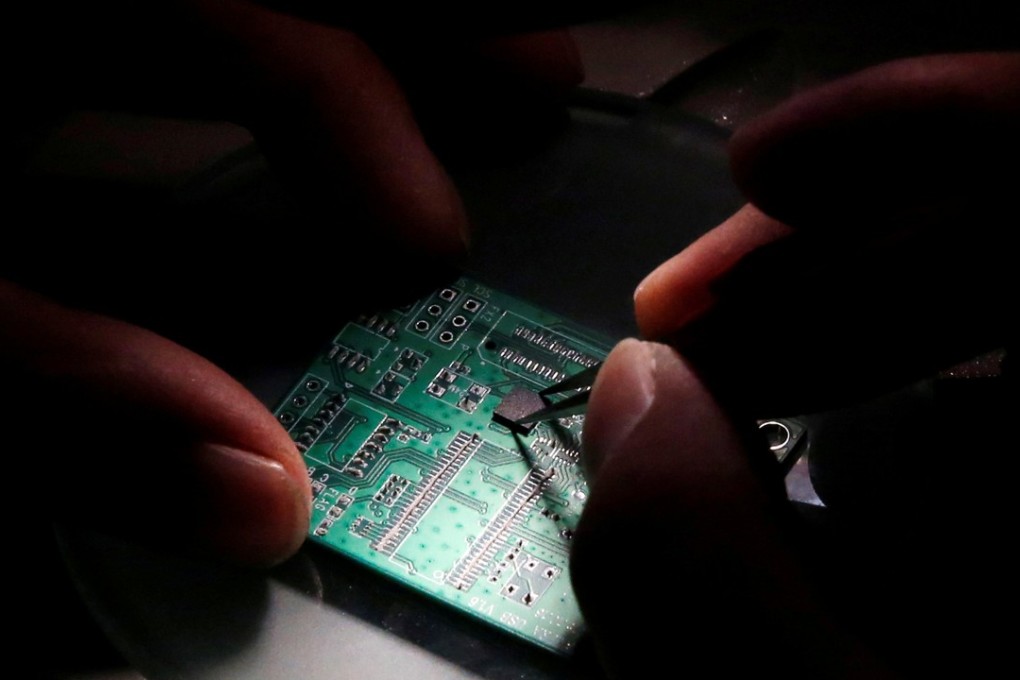
Super Micro has said it has found no malicious hardware in its products, in another effort to refute a news report that China’s intelligence services planted malicious chips in the company’s server motherboards.
The server maker, whose products were said to be compromised in a bombshell article by Bloomberg Businessweek magazine on October 4, said that, contrary to the report’s claim, no government agency had contacted the company about such hardware.
In a letter emailed to Florida Senator Marco Rubio and Connecticut Senator Richard Blumenthal – a copy of which was obtained by the South China Morning Post – Super Micro (also known as Supermicro) denied Bloomberg’s reports.
“We are confident the recent Bloomberg Businessweek stories are wrong,” wrote Perry Hayes, president of Super Micro Netherlands and its senior vice-president of investor relations.
“In fact, we believe that it is impossible as a practical matter to insert unauthorised malicious chips onto our boards during the manufacturing process.”