Chinese cybersecurity firm claims to have developed WannaCry virus ‘vaccine’
Rising, a firm that provides network security service to the Chinese government, says its vaccine will destroy ‘all known and future ransomware’
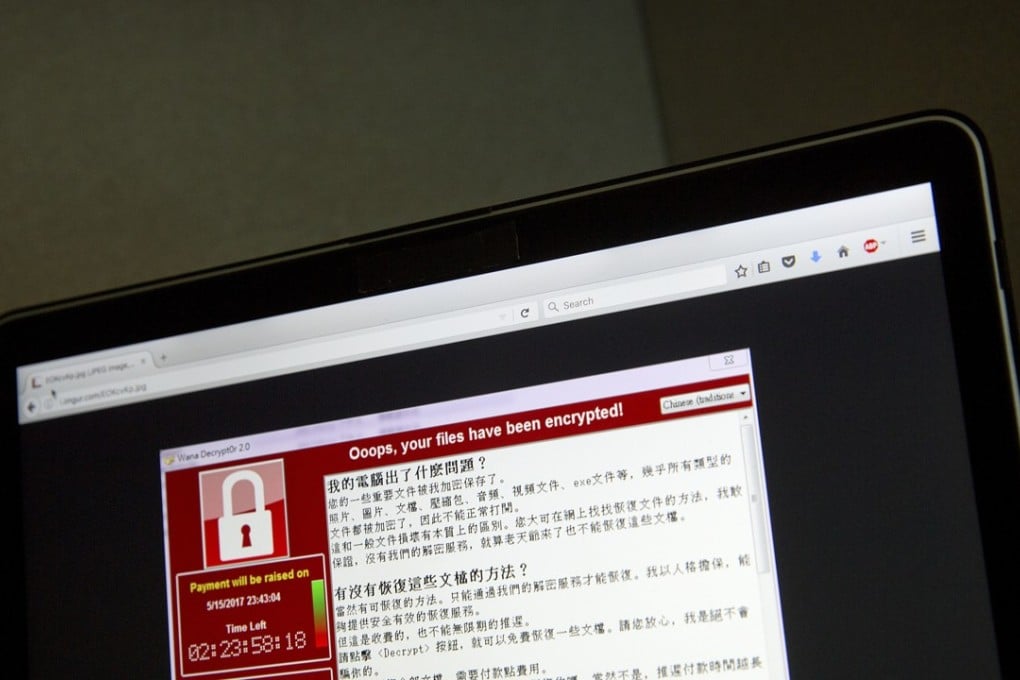
In the wake of the WannaCry global cyberattack, a Chinese cybersecurity firm claims to have developed a “vaccine” for all ransomware virus that will work even with new variants that have yet to surface.
Rising, which provides network security services to the Chinese government, released a free programme on its website on Friday that it said would protect computers from all ransomware, including the WannaCry worm that has affected companies, institutions and individuals around the world since last week.
Rising’s antivirus products are used in the Communist Party headquarters, State Council, Ministry of Public Security and other government agencies.

Tang Wei, the company’s vice-president, said Rising had analysed all the strains of all known ransomware using artificial intelligence and found that the malicious programmes shared up to 80 behavioural traits.
Rising’s “vaccine”, called Rising Sword, worked by presenting the virus with a “bait”, according to Tang.