Hi-tech hackers can exploit your office dinosaur, the fax machine, and all they need is the number
By sending an image file that contains malicious software over the phone line, hackers are able to take control of the device and access the rest of the network, experts warn

The fax machine is widely considered to be a dinosaur of inter-office communications, but it may also present a vulnerable point where hackers can infiltrate an organisation’s network, according to a new report from Israel-based software company Check Point.
The company said that the vulnerability was identified as a result of research intended to discover potential security risks, and not as the result of any attack.
The report estimates that there are still more that 17 million fax machines in use in the United States alone. The legal and medical fields both continue to rely heavily on fax machines to conduct business, since they are widely considered to be a more secure form of transmitting sensitive information and signatures compared to email. Banking and real estate also frequently transfer documents containing signatures via fax.
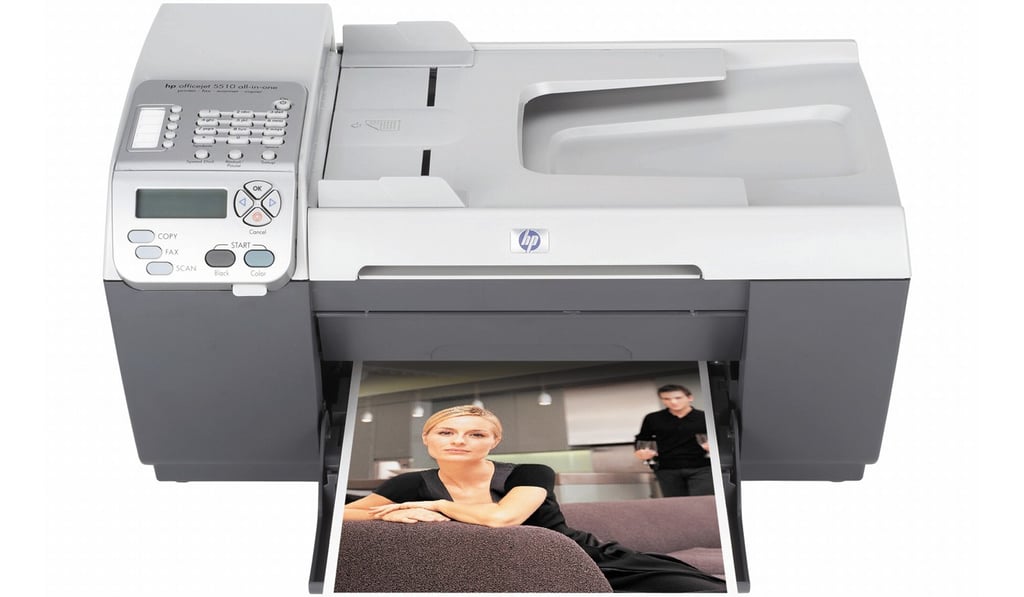
With the advent of all-in-one products that include fax functions as well as printing and scanning, fax machines may be more prevalent in homes and office than people realise. This particular vulnerability only applies if such a machine is connected to a telephone line, however.
The only machines tested were from HP’s line of all-in-one printers, but according to the report, these vulnerabilities are likely to be found in machines from any manufacturer that use similar technology. HP issued a patch for its products before the report was published, which is available for download from its support website.