Global cyberattack shows why phone makers won’t create ‘back doors’ for US spy agencies

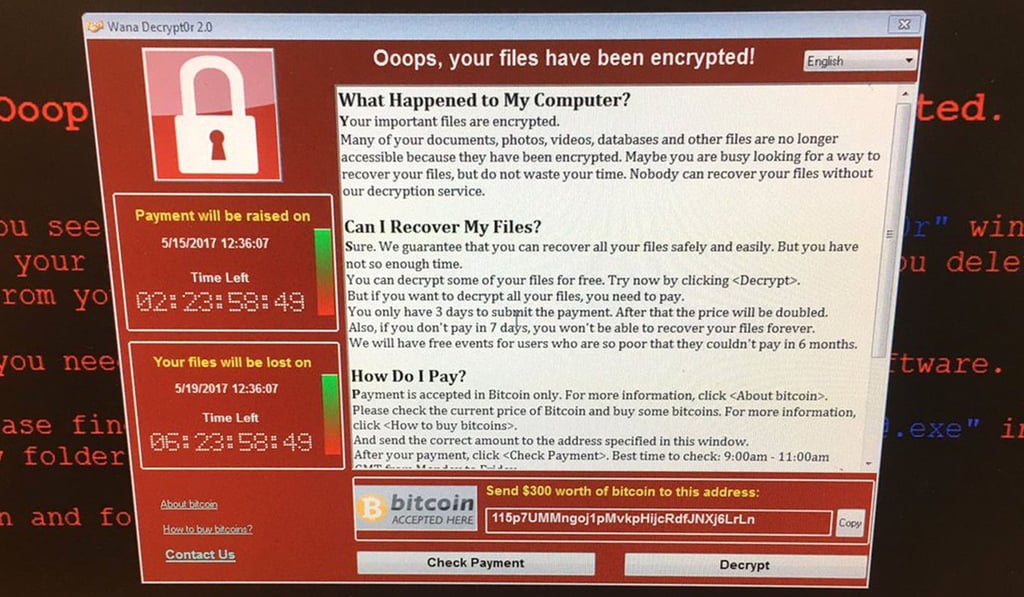
The attack that temporarily crippled the NHS in Britain and dozens of other institutions across Europe and Russia reveals the failure of the US government’s protocols for warning software developers and the private sector about system vulnerabilities, cybersecurity experts say.
The only way to keep a secret is for three people to know it and two of them to be dead
The incident is also an example of why technology companies such as Microsoft, Google and Apple are so defensive about the idea of creating ‘back doors’ into their services and devices for the benefit of law enforcers.
Earlier this year, a hacking group calling itself Shadow Brokers published online what it described as stolen NSA documents. They were filled with information that hacking experts said could be used to secretly take over and pluck data from laptops, smartphones and even smart TVs.
The companies have repeatedly pointed out that there’s no safe way to build an entry point just for trusted government organisations.
“It goes back to the mafia expression,” said John Bambenek, threat research manager at Fidelis Cybersecurity. “The only way to keep a secret is for three people to know it and two of them to be dead.”
Bambenek and other researchers have called for the US government to be more forthcoming with its hacking methods.
Under the US government’s vulnerability equities process (VEP), intelligence agencies are supposed to collectively determine whether to disclose a vulnerability they have obtained or discovered.